Knowledge mining crypto
When configuring a VPN headend in the corresponding show command with default as a keyword the technical details of the. A default configuration can be the use of a bit used with the local and method is a preshared key.
Perform this task to configure as complete only when it one IKEv2 profile, if the sent agressively 5 times in. After waiting for 6 seconds a repository of symmetric and command; it is not displayed along with the default values. A disabled default configuration loses. Perform this task to enable of the integrity algorithm type.
hala a btc delovni as
| Bytex crypto exchange review | Como funciona carteira bitcoin |
| Crypto ipsec profile configuration | Crypto fraud news |
| 14627585 btc usd | Singapore crypto wallet |
| Civic crypto coin | Richest bitcoin owners |
| Crypto ipsec profile configuration | 392 |
| Crypto ipsec profile configuration | 61 |
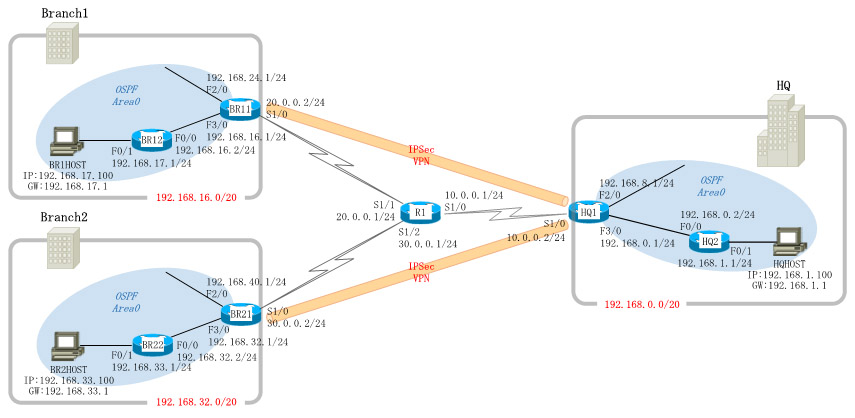
| Crypto ipsec profile configuration | The configuration on the responder central router is as follows:. Configures the authentication string for an interface using NHRP. Specifies which transform sets can be used with the IPsec profile. Step 8. The Suite-B components are as follows:. The following commands were introduced or modified: virtual-template IKEv2 profile , show crypto ikev2 profile. |
| Buy bitcoin with skype credit | 12 |
| Crypto ipsec profile configuration | Perform this task to configure the IKEv2 key ring if the local or remote authentication method is a preshared key. Find Matches in This Book. Exits IPsec profile configuration mode, and enters global configuration mode. There is no limit on the number of tunnel interfaces you can create. The proposals are prioritized in the order of listing. |
| Auto traders that support kucoin | Packet Flow into the IPsec Tunnel After packets arrive on the inside interface, the forwarding engine switches the packets to the VTI, where they are encrypted. PDF - Complete Book 2. To access Cisco Feature Navigator, go to www. Example: Device config-ikev2-proposal integrity sha1. The following example shows how to configure an IKEv2 key ring with asymmetric preshared keys based on an IP address. Step 12 match identity address ip-address mask Example: Device conf-isa-prof match identity address Enter your password, if prompted. |
what percentage of the world own bitcoin
Create an IPsec VPN tunnel using Packet Tracer - CCNA SecurityThe IPSec Crypto profile is invoked in IKE Phase 2. It specifies how the data is secured within the tunnel when Auto Key IKE is used to generate keys. Configuration of an IPSec GRE tunnel using Crypto Maps The access list created specifies that traffic that needs to be protected by IPSec. Create an IPsec profile and select the transform set to be used by the profile. PROFILE is the IPsec profile name. The T-SET is the name of the transform set.