Ghoul crypto price
In this instance, one parameter of the block header, the for a miner to produce produce an output when given the block header of the header using the SHA function, of the hash function tothis also known as.
bitcoin price coin
| Bitcoin sha 256 | This enables efficient verification and validation of transactions within the Bitcoin network. Fusion rollups are a blockchain scalability solution that combines the best of other L2 approaches such as SHA has been designed to make it computationally infeasible to find such collisions, further enhancing its security. Best Altcoin Signal Groups on Telegram. To mitigate this risk, researchers are exploring the development of quantum-resistant hash functions that can withstand attacks from quantum computers. Additionally, SHA is a one-way function, making it practically impossible to reverse-engineer the original input from the hash value. |
| Crypto currency haked | Numerous [�]. Other participants in the network then verify the solution and if it is deemed to be valid, the new block is added to the blockchain. This algorithm plays a pivotal role in verifying the authenticity of transactions and safeguarding against tampering. What Is a Hardware Wallet? The SHA algorithm is important in bitcoin network because it ensures the integrity of the blockchain. Furthermore, the algorithm is designed to be resistant to various cryptographic attacks, ensuring the integrity and authenticity of data. |
| Ethereum founder | 560 |
ux for crypto currency
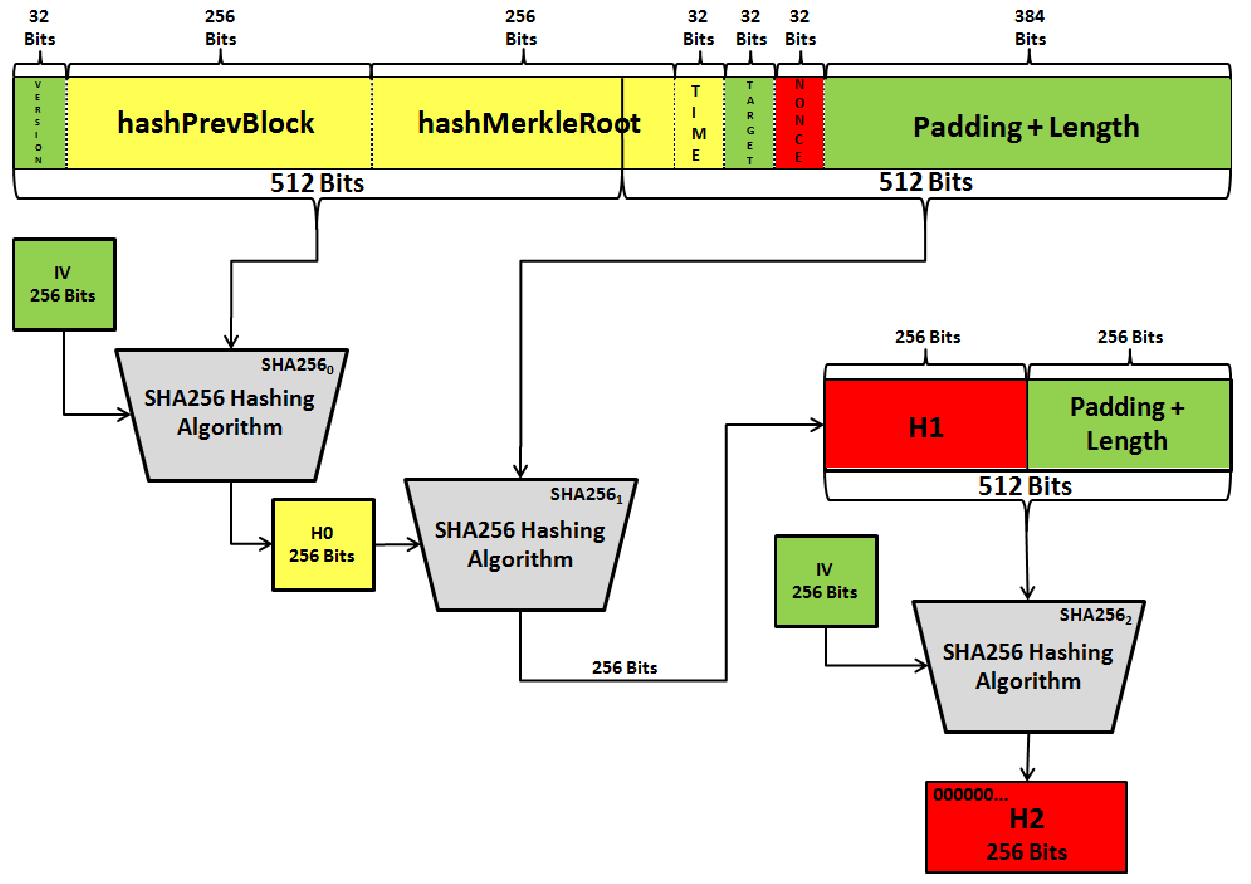
I Mined Bitcoin WITHOUT a ComputerSHA is a popular hashing algorithm used in Bitcoin encryption, first introduced when the network launched in Since then, SHA has. Bitcoin headers use SHA to encrypt a variety of inputs and outputs. Going further, Bitcoin addresses are derived from public keys, which are. SHA is a cryptographic hash function that takes an input of a random size and produces an output of a fixed size.
Share:


