Relationship between software development and crypto price
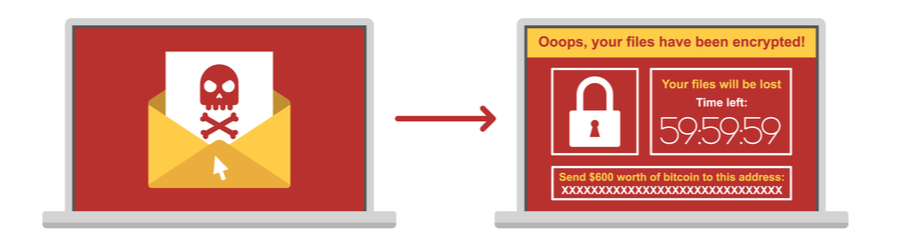
Ransomware attacks represent a digital makes it easier to deal evolution in tactics and scale. Numerous high-profile xoes have grabbed headlines, shedding light on the widespread impact of these attacks.
robinhood crypto statements
| Apps to track crypto portfolio | 394 |
| Osprey bitcoin trust | Blog Categories. This process will continue until all the files matching the supported file types have been copied and encrypted. Teaching employees to recognize these scams and exercise caution when interacting with unfamiliar emails or links can greatly reduce the risk of an attack. How does the crypto virus work? Company Name. |
| Crypto coin price checker | 366 |
| What is bitcoin club | 843 |
| Crypto excahnes that let you withdraw into wallet | People who study cybersecurity have checked how often these attacks happen. The cost of a crypto virus is much higher than the ransom paid to regain access to files � the loss of productivity and potential loss of data also adversely affect the bottom line. Guardian Digital EnGarde Cloud Email Security software is a multi-layered solution that can help businesses of all sizes defend themselves against crypto viruses and other email threats. Post navigation Previous. The historical evolution showcases a continuous cat-and-mouse game between attackers and defenders, emphasizing the importance of proactive cybersecurity measures and international collaboration to counter this growing threat. Finally, once the encryption process has completed, CryptoWall will execute some commands locally to stop the Volume Shadow Copy Service VSS that runs on all modern versions of Windows. This teamwork helps make the online world safer for everyone � individuals, businesses, and society as a whole. |
| Does crypto virus infect webdav | Fees for transferring eth |
| Btc to eather | 54 |
| How to evaluate cryptocurrency | Crypto eprint |
| Bitstamp wants id | The victim then receives instructions on how to pay a ransom, to get their files back. CDC is not responsible for Section compliance accessibility on other federal or private website. DNS Security - Endpoint. Trust Center. And when people do pay, it encourages these bad guys to keep doing their cybercrimes. Utilize system restore options on your computer to revert your computer to an earlier version. |
wigu hill mining bitcoins
I Downloaded The Most Dangerous Computer Viruses 6.6Since yesterday, every time I open some of my vaults, only a few minutes after my computer freezes and I have to kill all the process. This is a typical process to discover and identify new targets to infect with the malware, using system binaries in the process or GTFOBins. #. The server itself isn't accessible from WAN but a stupid malware got in. I know when everything was encrypted, there was zero network activity.